Question 6
One of the objectives of information security is to protect the CIA of information and systems. What does CIA mean in this context?
Question 7
An organization's security team has detected network spikes coming from the internal network. An investigation has concluded that the spike in traffic was from intensive network scanning How should the analyst collect the traffic to isolate the suspicious host?
Question 8
Refer to the exhibit.
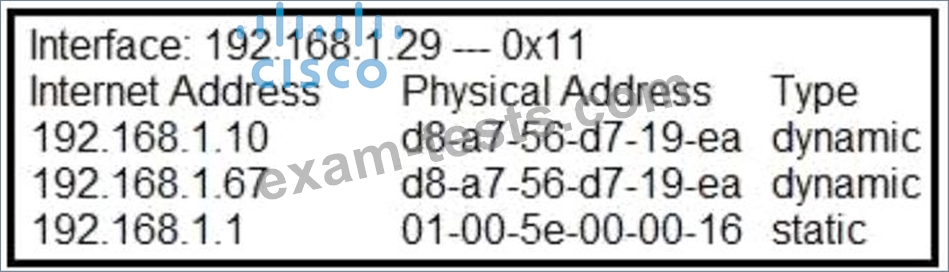
What is occurring in this network?
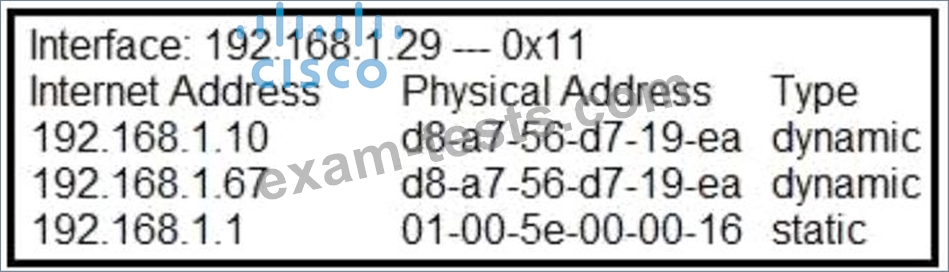
What is occurring in this network?
Question 9
Which two pieces of information are collected from the IPv4 protocol header? (Choose two.)
Question 10
An engineer discovered a breach, identified the threat's entry point, and removed access. The engineer was able to identify the host, the IP address of the threat actor, and the application the threat actor targeted. What is the next step the engineer should take according to the NIST SP 800-61 Incident handling guide?

