Question 51
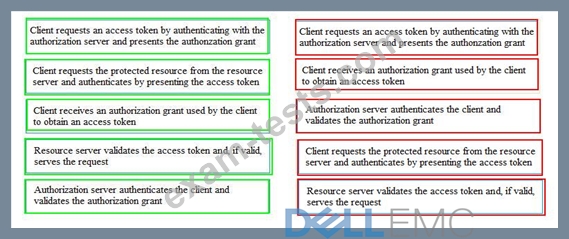
If the client requests authorization from the resource owner, what are the remaining sequence of steps to authenticate a user using OAuth control?

1. The client requests authorization from the resource owner. The authorization request can be made directly to the resource owner, or indirectly through the authorization server.
2. The client receives an authorization grant, which is a credential representing the resource owner's authorization to access its protected resources. It is used by the client to obtain an access token. Access tokens are credentials that are used to access protected resources. An access token is a string representing an authorization issued to the client. The string is usually opaque to the client. Tokens represent specific scopes and durations of access, granted by the resource owner, and enforced by the resource server and authorization server.
3. The client requests an access token by authenticating with the authorization server and presenting the authorization grant.
4. The authorization server authenticates the client and validates the authorization grant, and if valid, issues an access token.
5. The client requests the protected resource from the resource server and authenticates by presenting the access token.
6. The resource server validates the access token, and if valid, serves the request.

1. The client requests authorization from the resource owner. The authorization request can be made directly to the resource owner, or indirectly through the authorization server.
2. The client receives an authorization grant, which is a credential representing the resource owner's authorization to access its protected resources. It is used by the client to obtain an access token. Access tokens are credentials that are used to access protected resources. An access token is a string representing an authorization issued to the client. The string is usually opaque to the client. Tokens represent specific scopes and durations of access, granted by the resource owner, and enforced by the resource server and authorization server.
3. The client requests an access token by authenticating with the authorization server and presenting the authorization grant.
4. The authorization server authenticates the client and validates the authorization grant, and if valid, issues an access token.
5. The client requests the protected resource from the resource server and authenticates by presenting the access token.
6. The resource server validates the access token, and if valid, serves the request.
Question 52
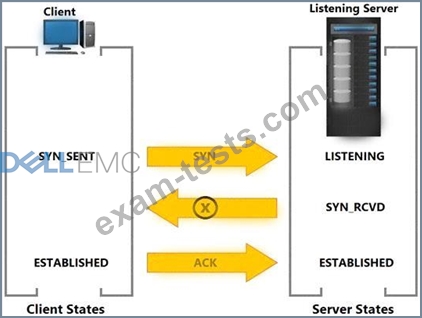
Based on the exhibit, what does the "X" represent?
Question 53
Which Converged Network Adapter (CNA) component encapsulates Fibre Channel (FC) frames into Ethernet frames?
Question 54
Why should a replica be consistent with its source?
Question 55
In an FCoE environment, which functionality provides a framework for the allocation of bandwidth to different network traffic classes?