Question 56
The incident response team was notified of detected malware. The team identified the infected hosts, removed the malware, restored the functionality and data of infected systems, and planned a company meeting to improve the incident handling capability. Which step was missed according to the NIST incident handling guide?
Question 57
An engineer returned to work and realized that payments that were received over the weekend were sent to the wrong recipient. The engineer discovered that the SaaS tool that processes these payments was down over the weekend. Which step should the engineer take first?
Question 58
A patient views information that is not theirs when they sign in to the hospital's online portal. The patient calls the support center at the hospital but continues to be put on hold because other patients are experiencing the same issue. An incident has been declared, and an engineer is now on the incident bridge as the CyberOps Tier 3 Analyst. There is a concern about the disclosure of PII occurring in real-time. What is the first step the analyst should take to address this incident?
Question 59
Employees report computer system crashes within the same week. An analyst is investigating one of the computers that crashed and discovers multiple shortcuts in the system's startup folder. It appears that the shortcuts redirect users to malicious URLs. What is the next step the engineer should take to investigate this case?
Question 60
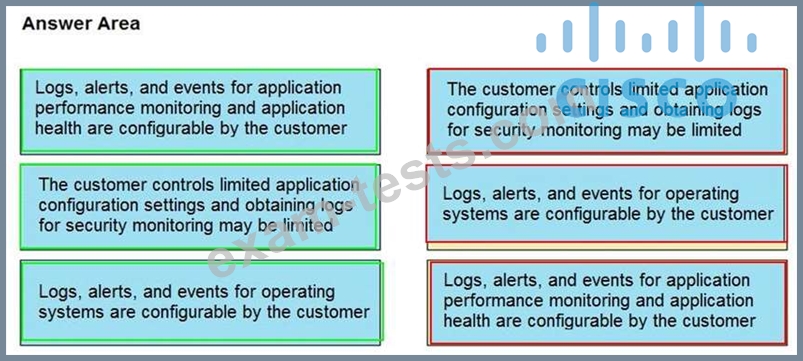
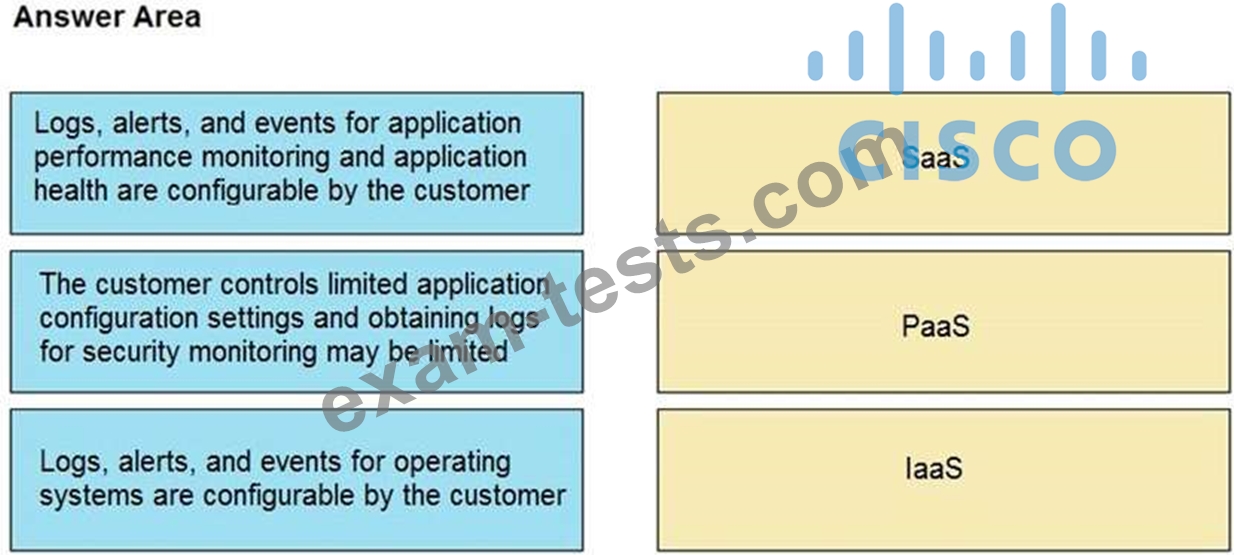
Drag and drop the telemetry-related considerations from the left onto their cloud service models on the right.
Premium Bundle
Newest 350-201 Exam PDF Dumps shared by BraindumpsPass.com for Helping Passing 350-201 Exam! BraindumpsPass.com now offer the updated 350-201 exam dumps, the BraindumpsPass.com 350-201 exam questions have been updated and answers have been corrected get the latest BraindumpsPass.com 350-201 pdf dumps with Exam Engine here: