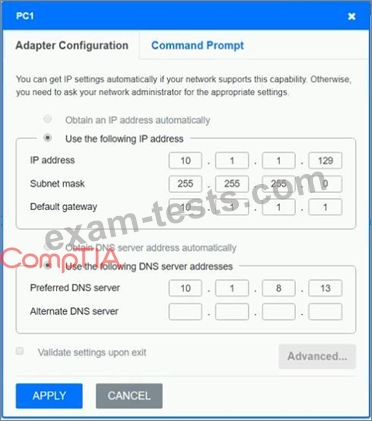
Question 101
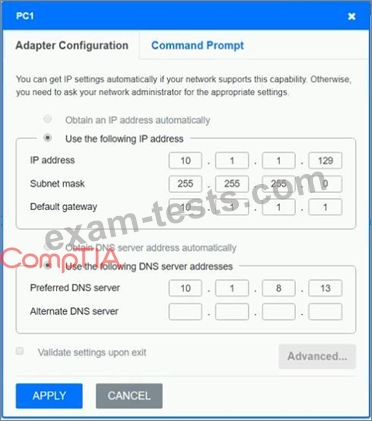
After recent changes to the pictured network, several users are unable to access the servers. Only PC1, PC2, PC3, and PC4 are clickable and will give you access to the command prompt and the adapter configuration tabs.
INSTRUCTIONS
Verify the settings by using the command prompt, after making any system changes.
Next, restore connectivity by making the appropriate changes to the infrastructure.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.





INSTRUCTIONS
Verify the settings by using the command prompt, after making any system changes.
Next, restore connectivity by making the appropriate changes to the infrastructure.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.





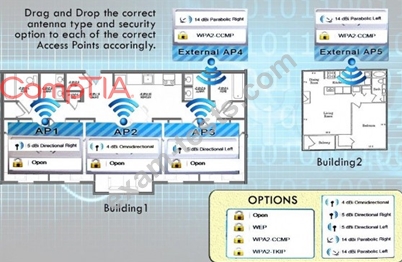
Question 102
Your company recently purchased a new building down the street from the existing office. For each of the tasks below, select the appropriate antenna type and encryption object for all wireless access point (AP).
1. Create an encrypted wireless connection between the two buildings that BEST controls signal propagation, while maximizing security.
2. Restrict the wireless signal generated by the access points (APs) inside Building 1, so that it minimizes broadcast beyond the building.
3. Maximize wireless coverage inside Building 1.
4. Building 1's internal wireless network is for visitors only and must not require any special configuration on the visitor's device to connect.
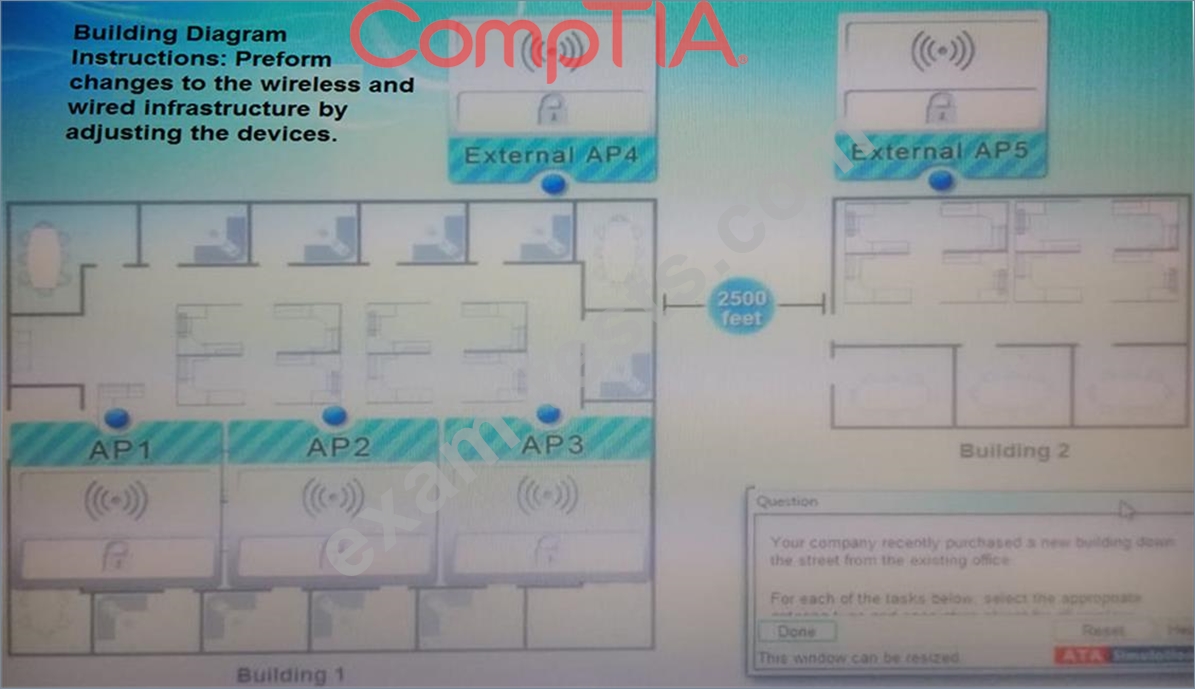
Instructions: When you have completed the simulation, select the Done button to submit.
1. Create an encrypted wireless connection between the two buildings that BEST controls signal propagation, while maximizing security.
2. Restrict the wireless signal generated by the access points (APs) inside Building 1, so that it minimizes broadcast beyond the building.
3. Maximize wireless coverage inside Building 1.
4. Building 1's internal wireless network is for visitors only and must not require any special configuration on the visitor's device to connect.
Instructions: When you have completed the simulation, select the Done button to submit.
Question 103
A network technician has provisioned a new Linux instance in public cloud provider's IaaS environment. The technician did not install a graphical user interface. The technician wants to connect to the server's public IP address securely to start a console session. Which of the following remote access methods should the technician use?
Question 104
A Chief Information Security Officer (CISO) has decided to implement a secure and user-friendly way to connect to the corporate wireless network Each workstation will be authenticated individually using a unique certificate that will be deployed to the workstation by the organization's certificate authority. Which of the following authentication methods would meet this requirement?
Question 105
A network technician wants to gain a better understanding of network trends to determine if they are over capacity. Which of the following processes should the technician use?