Question 66
A development team has asked users to conduct testing to ensure an application meets the needs of the business. Which of the fallowing types of testing docs This describe?
Question 67
A security analyst has received reports of very slow, intermittent access to a public-facing corporate server. Suspecting the system may be compromised, the analyst runs the following commands:
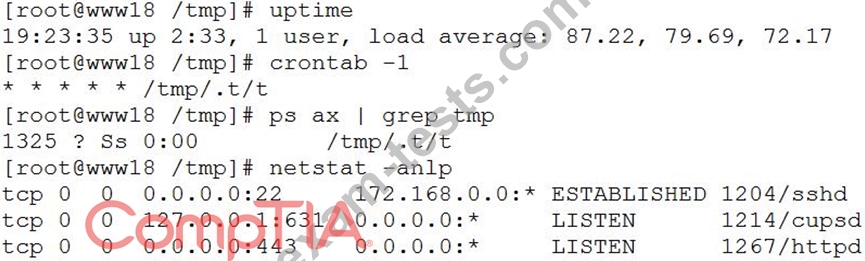
Based on the output from the above commands, which of the following should the analyst do NEXT to further the investigation?
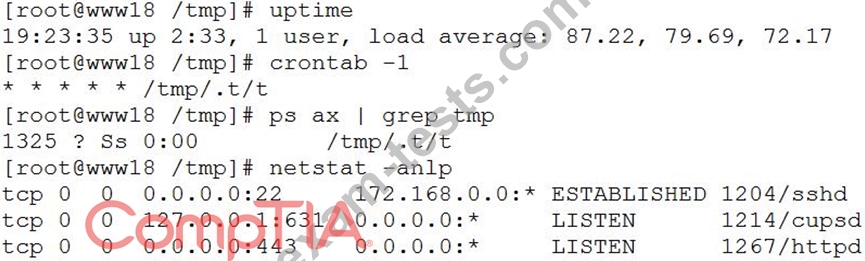
Based on the output from the above commands, which of the following should the analyst do NEXT to further the investigation?
Question 68
A remote code execution vulnerability was discovered in the RDP. An organization currently uses RDP for remote access to a portion of its VDI environment. The analyst verified network-level
authentication is enabled
Which of the following is the BEST remediation for this vulnerability?
authentication is enabled
Which of the following is the BEST remediation for this vulnerability?
Question 69
It is important to parameterize queries to prevent:
Question 70
Ann, a user, reports to the security team that her browser began redirecting her to random sites while using her Windows laptop. Ann further reports that the OS shows the C: drive is out of space despite having plenty of space recently. Ann claims she not downloaded anything. The security team obtains the laptop and begins to investigate, noting the following:
File access auditing is turned off.
When clearing up disk space to make the laptop functional, files that appear to be cached web pages are immediately created in a temporary directory, filling up the available drive space.
All processes running appear to be legitimate processes for this user and machine.
Network traffic spikes when the space is cleared on the laptop.
No browser is open.
Which of the following initial actions and tools would provide the BEST approach to determining what is happening?
File access auditing is turned off.
When clearing up disk space to make the laptop functional, files that appear to be cached web pages are immediately created in a temporary directory, filling up the available drive space.
All processes running appear to be legitimate processes for this user and machine.
Network traffic spikes when the space is cleared on the laptop.
No browser is open.
Which of the following initial actions and tools would provide the BEST approach to determining what is happening?

