Question 91
After attempting to harden a web server, a security analyst needs to determine if an application remains vulnerable to SQL injection attacks. Which of the following would BEST assist the analyst in making this determination?
Question 92
An organization uses application whitelisting to help prevent zero-day attacks. Malware was recently identified on one client, which was able to run despite the organization's application whitelisting approach. The forensics team has identified the malicious file, conducted a post-incident analysis, and compared this with the original system baseline. The team sees the following output:
filename hash (SHA-1)
original: winSCP.exe 2d da b1 4a 98 fc f1 98 06 b1 e5 26 b2 df e5 f5 3e cb 83 el latest: winSCP.exe a3 4a c2 4b 85 fa f2 dd 0b ba f4 16 b2 df f2 4b 3f ac 4a e1 Which of the following identifies the flaw in the team's application whitelisting approach?
filename hash (SHA-1)
original: winSCP.exe 2d da b1 4a 98 fc f1 98 06 b1 e5 26 b2 df e5 f5 3e cb 83 el latest: winSCP.exe a3 4a c2 4b 85 fa f2 dd 0b ba f4 16 b2 df f2 4b 3f ac 4a e1 Which of the following identifies the flaw in the team's application whitelisting approach?
Question 93
A critical enterprise component whose loss or destruction would significantly impede business operations or have an outsized impact on corporate revenue is known as:
Question 94
A company's user lockout policy is enabled after five unsuccessful login attempts. The help desk notices a user is repeatedly locked out over the course of a workweek. Upon contacting the user, the help desk discovers the user is on vacation and does not have network access. Which of the following types of attacks are MOST likely occurring? (Choose two.)
Question 95
A hacker has a packet capture that contains:
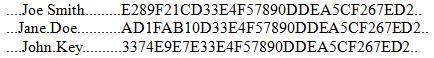
Which of the following tools will the hacker use against this type of capture?
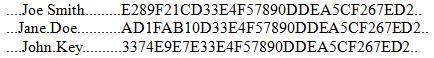
Which of the following tools will the hacker use against this type of capture?

