Question 41
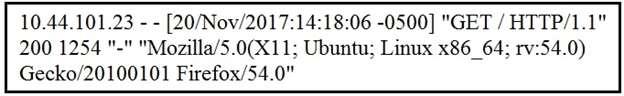
Refer to the exhibit. What does the message indicate?
Question 42
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?
Question 43
Which tool provides a full packet capture from network traffic?
Question 44
A security expert is working on a copy of the evidence, an ISO file that is saved in CDFS format. Which type of evidence is this file?
Question 45
What is an attack surface as compared to a vulnerability?

