Question 26
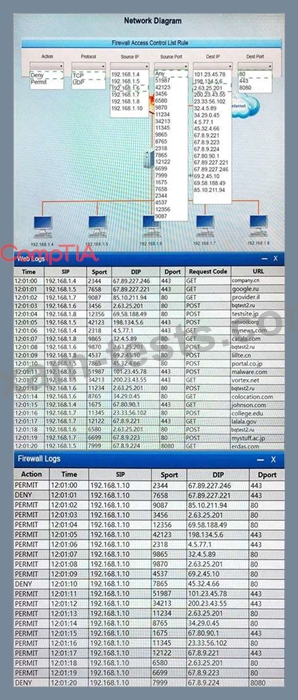
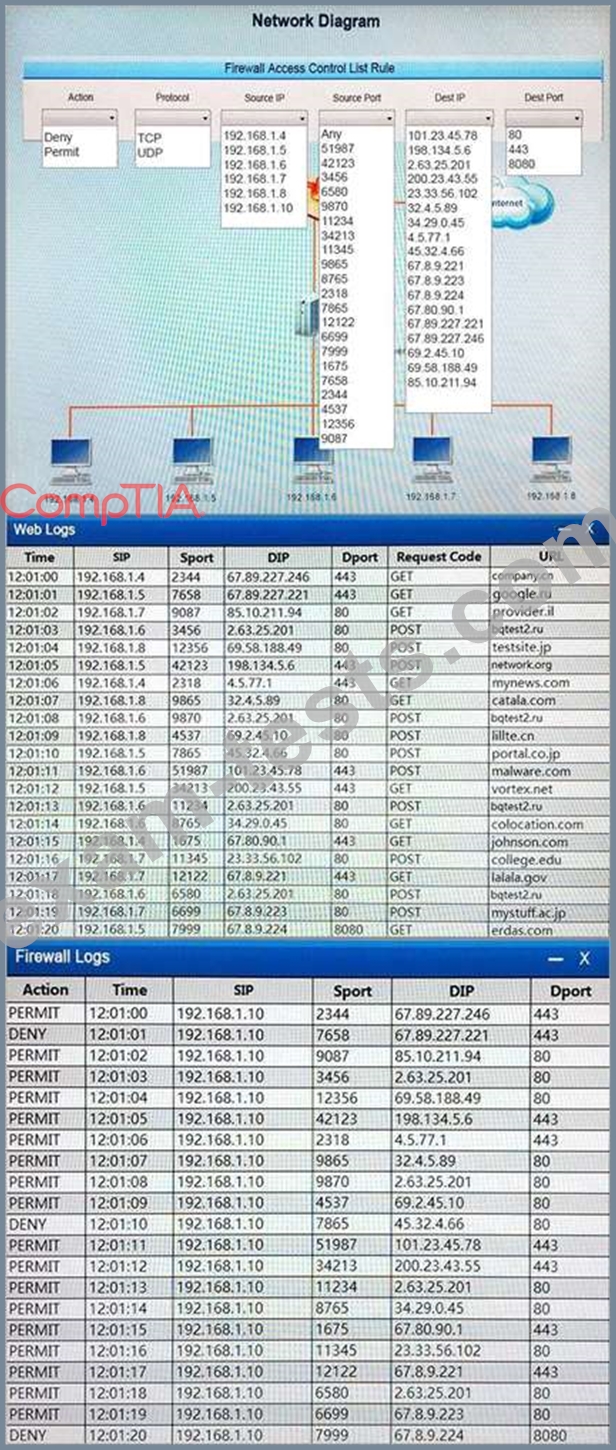
A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company's web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization.
Instructions:
Modify the firewall ACL, using the Firewall ACL form to mitigate the issue.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
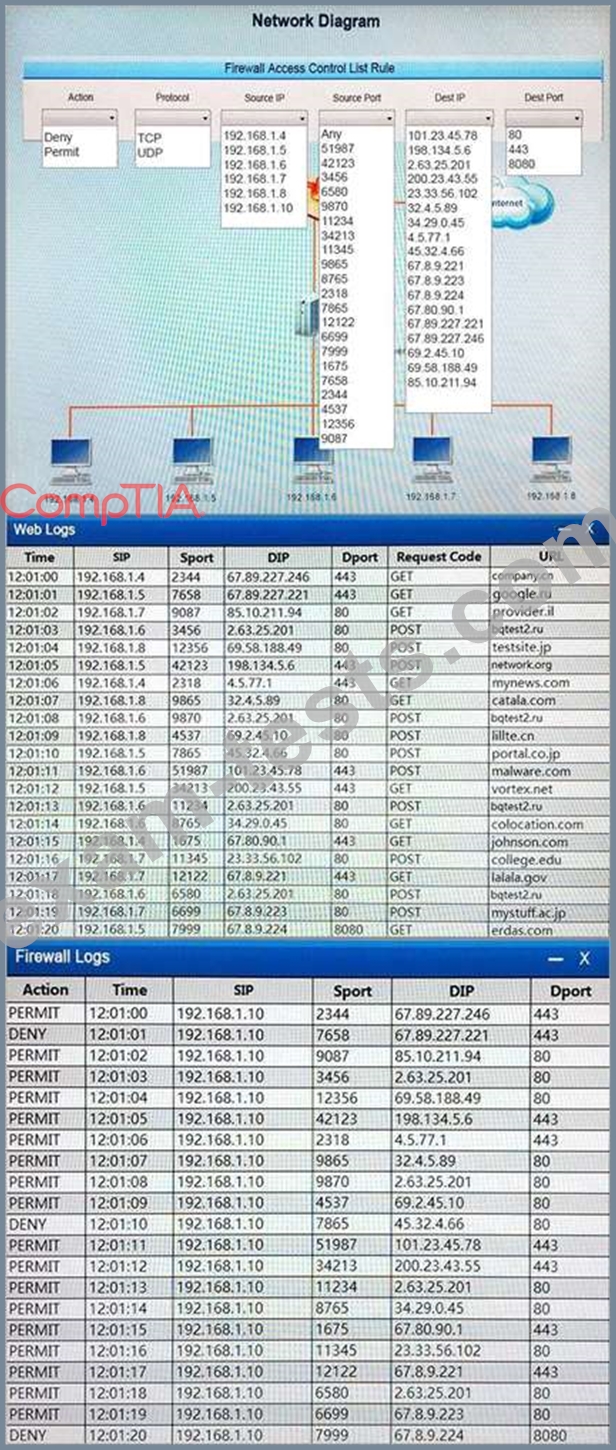
Instructions:
Modify the firewall ACL, using the Firewall ACL form to mitigate the issue.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
Question 27
Which of the following are essential components within the rules of engagement for a penetration test?
(Select TWO).
(Select TWO).
Question 28
A software assurance lab is performing a dynamic assessment on an application by automatically generating and inputting different, random data sets to attempt to cause an error/failure condition. Which of the following software assessment capabilities is the lab performing AND during which phase of the SDLC should this occur? (Select two.)
Question 29
Which of the following tools should an analyst use to scan for web server vulnerabilities?
Question 30
Company A's security policy states that only PKI authentication should be used for all SSH accounts. A security analyst from Company A is reviewing the following auth.log and configuration settings:
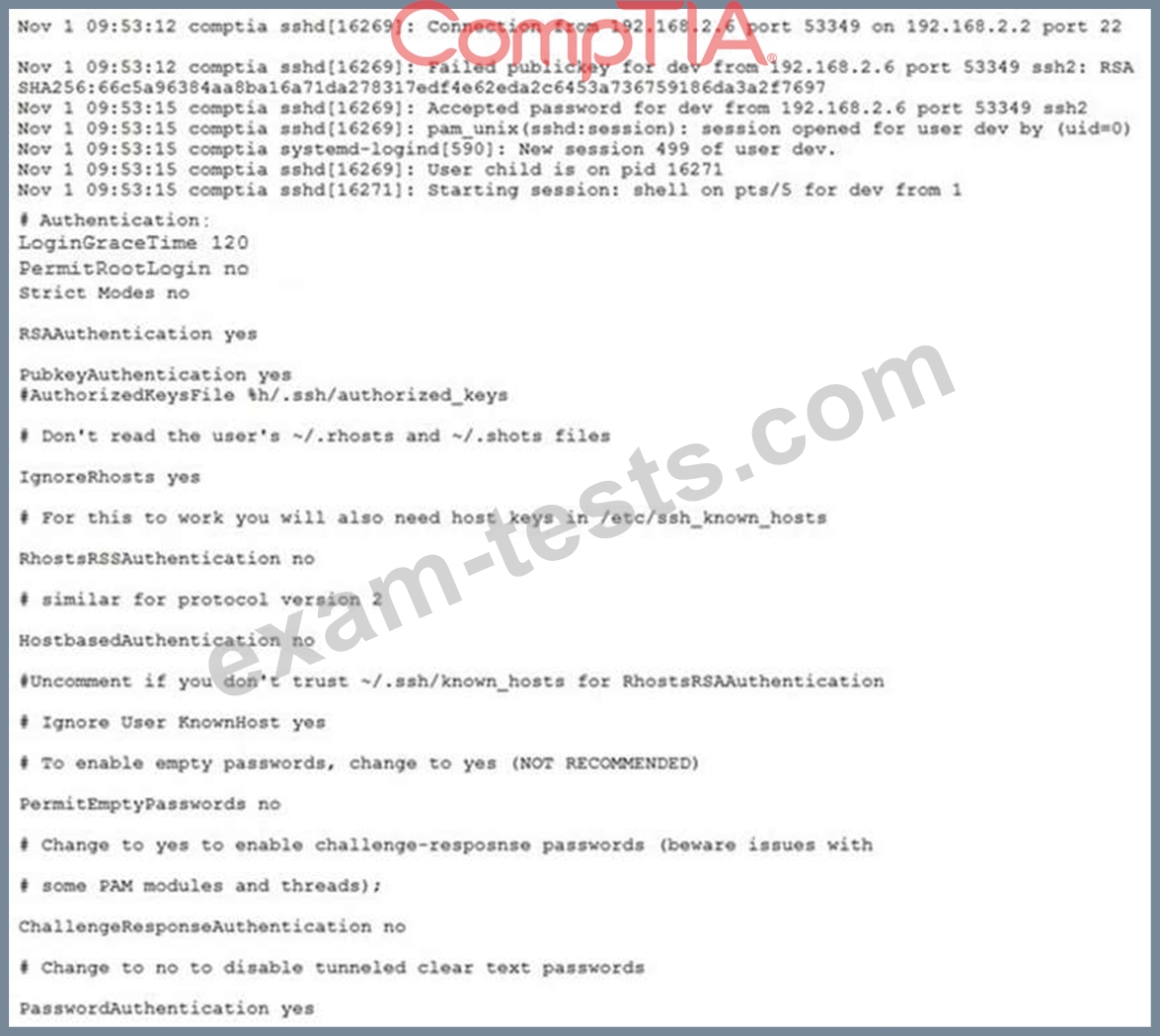
Which of the following changes should be made to the following sshd_config file to establish compliance with the policy?
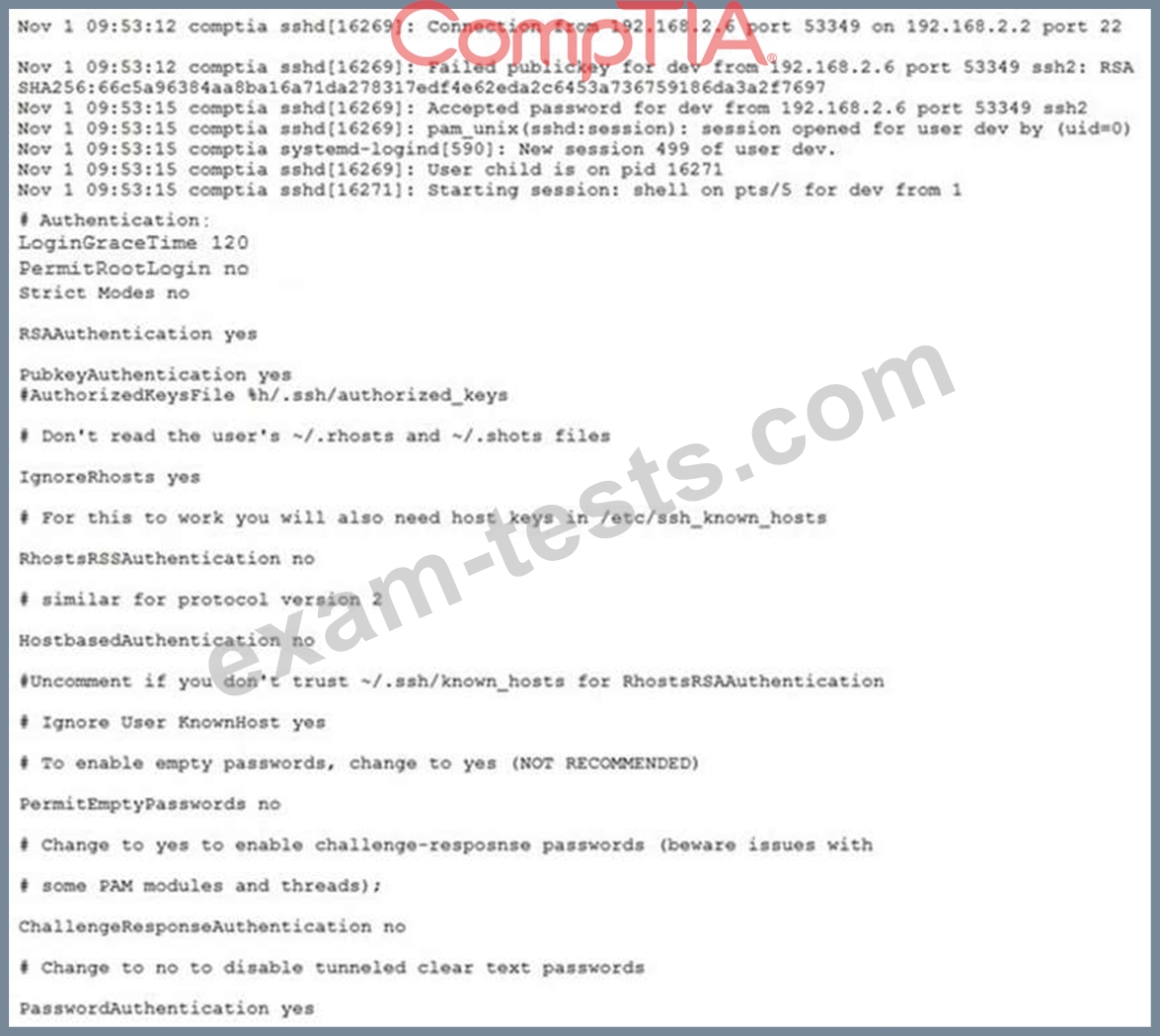
Which of the following changes should be made to the following sshd_config file to establish compliance with the policy?